WLAN: Unterschied zwischen den Versionen
Tine (Diskussion | Beiträge) KKeine Bearbeitungszusammenfassung |
|||
| Zeile 3: | Zeile 3: | ||
This is one reason why we want to use 802.1x with EAP-TTLS. Every member has it's own username/password combination which can be reset or changed through a webinterface. If a member quits the space, we just have to deactivate the account and the internal access is gone. | This is one reason why we want to use 802.1x with EAP-TTLS. Every member has it's own username/password combination which can be reset or changed through a webinterface. If a member quits the space, we just have to deactivate the account and the internal access is gone. | ||
The other reason is: Every member has | The other reason is: Every member has its own encrypted channel to our access points. In addition the member has the possibility to check, if the SSID can be trusted (avoid roque APs) with an ssl certificate | ||
== certificate == | == certificate == | ||
| Zeile 17: | Zeile 17: | ||
<syntaxhighlight line enclose="div"> | <syntaxhighlight line enclose="div"> | ||
Description='backspace WPA2 802.1X' | Description='backspace WPA2 802.1X' | ||
Interface= | Interface=wlp3s0s | ||
Connection=wireless | Connection=wireless | ||
Security=wpa-configsection | Security=wpa-configsection | ||
Version vom 6. Februar 2016, 15:39 Uhr
We're moving our wifi infrastructure to an authenticated and encrypted ssid. At the moment it's hard to change our internal wifi password, because our door system depends on it. If you are not in our internal wifi you can't operate the door.
This is one reason why we want to use 802.1x with EAP-TTLS. Every member has it's own username/password combination which can be reset or changed through a webinterface. If a member quits the space, we just have to deactivate the account and the internal access is gone.
The other reason is: Every member has its own encrypted channel to our access points. In addition the member has the possibility to check, if the SSID can be trusted (avoid roque APs) with an ssl certificate
certificate
To check if you're connecting to the correct SSID, you can and shoukd add the ssl certificate to your connection setting. You can download the SSL Certificate from our Server.
Warning: The certificate expires every two years. You can also check against the StartSSL G2 certificate which is much longer valid.
netctl
Save config as /etc/netctl/$interfacename-backspace_8021x. You have to restart netctl-auto (e.g. systemctl restart netctl-auto@$interface)
Description='backspace WPA2 802.1X'
Interface=wlp3s0s
Connection=wireless
Security=wpa-configsection
IP=dhcp
ESSID="backspace 802.1x"
WPAConfigSection=(
'ssid="backspace 802.1x"'
'proto=RSN WPA'
'key_mgmt=WPA-EAP'
'eap=TTLS'
'identity="USERNAME"'
'password="YOUR_PASSWORD"'
'phase2="auth=PAP"'
)You can enable SSL certificate checking with 'ca_cert="/path/to/your/hackerspace-bamberg.de.crt"'. For the certificate look at Technische_Infrastruktur/WLAN#Certificate.
wpa_supplicant
Add to /etc/wpa_supplicant/wpa_supplicant.conf:
network={
ssid="backspace 802.1x"
key_mgmt=WPA-EAP
eap=TTLS
identity="USERNAME"
password="YOUR_PASSWORD"
phase2="auth=PAP"
}You can enable SSL certificate checking with ca_cert="/path/to/your/hackerspace-bamberg.de.crt". For the certificate look at Technische_Infrastruktur/WLAN#Certificate.
connman
UNTESTED!
[service_backspace]
Type=wifi
Name="backspace 802.1x"
EAP=ttls
Phase2=PAP
Identity=USERNAME
Passphrase=YOUR_PASSWORDwicd
ctrl_interface=/var/run/wpa_supplicant
network={
ssid="backspace 802.1x"
scan_ssid=$_SCAN
identity="USERNAME"
password="YOUR_PASSWORD"
proto=WPA2
key_mgmt=WPA-EAP
group=CCMP
pairwise=CCMP
eap=TTLS
anonymous_identity="$_ANONYMOUS_IDENTITY"
phase2="auth=PAP"
}You can enable SSL certificate checking with ca_cert="/path/to/the/hackerspace-bamberg.de.crt". For the certificate look at Technische_Infrastruktur/WLAN#Certificate.
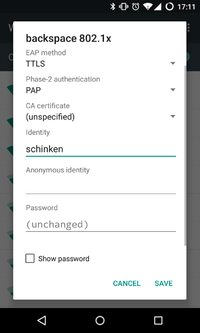
Android
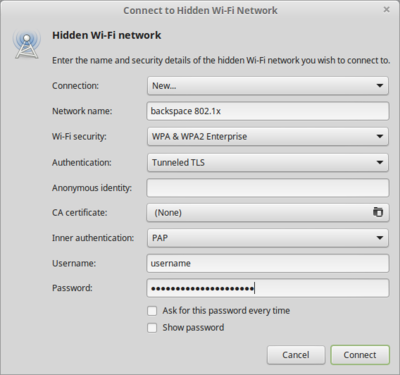
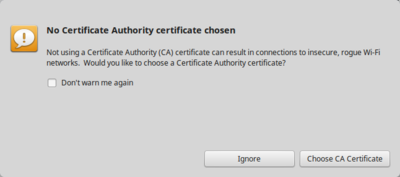
Linux - NetworkManager
Ignore the certificate warning as long as we don't provide a certificate.
Windows 7
Windows 7 does not support EAP-TTLS / PAP from scratch. The same is true for eduroam networks and this is why there are a lot of instructions from universities which use SecureW2 as an additional Software to enable EAP-TTLS:
TODO: Own instructions and screenshots
Windows 8 and above
Since Windows 8 the system itself is capable of EAP-TTLS.
TODO: Someone with windows should do some screenshots.